Encryption is one of those things not many people enjoy – mainly because it’s complicated! This is particularly true in regards to good encryption.
Thankfully, on most Linux distributions, a tool called GnuPG (gpg) comes pre-installed. However, you still need to generate your “keys”, and this is what confuses most would-be crypto users.
There are two main types of cryptography that will be covered here – symmetrical, and asymmetrical (also known as “public key cryptography”). This post is by no means an in-depth discussion on either. Instead, the objective here is to quickly get things set up so you can encrypt ’til your heart’s content. Still, each of these is worth a very brief and over-simplified explanation.
Symmetrical Cryptography
This is a form of cryptography where the same “key” (password) is used to both encrypt and decrypt plaintext.
Asymmetrical Cryptography
With asymmetrical cryptography (public key cryptography) there are two “keys” – a public key, and a private key. Either key can be used to encrypt data, but only the other key-pair is able to decrypt the resulting ciphertext (encrypted data). This means you can distribute your public key so that people can encrypt messages and send them to you, and only you will be able to decrypt them using your private key.
How awesome is that!!
Using GnuPG
Symmetrical Encryption
Symmetrical cryptography is the easier of the two:
Encrypt with:
gpg -c filename (or gpg --symmetric filename)
Decrypt with:
gpg -c filename (or gpg --symmetric filename)
If you are attempting to decrypt a file and do not supply the same password that was used to encrypt the file, then the operation will fail.
Asymmetrical Encryption
Generate Keys
gpg --gen-key
You will be able to accept the defaults where applicable, but you’ll still need to enter your real name, email address (which will be used to identify the keys that are generated), and an optional “paraphrase” for your private key. While the paraphrase is optional, it’s recommended you use one so that should your private key be compromised, it will be unusable. Circumstances where you may opt to not use a private key is on servers (for automated scripts).
Once your keys have been generated, you can actually encrypt files to yourself! Encrypting files to yourself is very handy if you have sensitive data you want to store in an untrusted environment, such as “the cloud”.
Import a Public Key
Remember that someone’s public key can be used to encrypt a file that only their private key can decrypt. Before you can encrypt a file to send to another recipient, you first need to import their public key.
gpg --import <filename>
Verify and Sign an Imported Public Key
Once you have imported a public key, you can verify and sign it.
gpg --fingerprint <key_id>
Compare the public key’s fingerprint with the key’s owner (it will probably be published on a key server, or you can ask them directly). If the fingerprints match and you’re sure their public key hasn’t been tampered with, sign it:
gpg --sign-key <key_id>
List Keys
gpg --list-keys
Or to list a specific key:
gpg --list-key <key_id>
(the key_id can be the email address entered when generating the key).
Backing Up Keys
One easy way to backup everything is to simply tar up and encrypt your ~/.gnupg directory:
$ tar -czvf my-gnupg.tar.gz ~/.gnupg $ gpg -c my-gnupg.tar.gz
Make sure you enter a good password. You can then store the resulting my-gnupg.tar.gz.gpg in your preferred cloud drive (for example, Google Drive).
The other option is to use GnuPG to export private key. If you lose your private key, you will never be able to decrypt anything that has been encrypted with your public key! For this reason, it is important that you securely backup your private key.
$ gpg -ao my-private.key --export-secret-keys <key_id> $ gpg -c my-private.key
(then store my-private.key somewhere safe).
Exporting your Public Key
For someone to be able to send you encrypted data, they first need your public key. You can export your public key to a file using:
gpg -ao my-public.key --export your_email@address.com
You can then publish my-public.key (or send it to whoever wishes to send you encrypted data).
Encrypting and Decrypting Files
Finally, the fun part! After setting up your public/private keypair (and perhaps importing third-party public keys), you’re now ready to encrypt away. As mentioned above, you could perform this step immediately after generating your keys.
Encrypting a File
gpg -e filename
Encrypt and Sign a File
Signing is a way to make sure the file that has been encrypted has not been tampered with.
gpg -es filename
Encrypt for Multiple Recipients
Using multiple recipients allows multiple people (keys) to decrypt the encrypted file:
gpg -es -r john@google.com -r jane@yahoo.com backup.tar.gz
From the above example, both John and Jane can use their private keys to decrypt backup.tar.gz.gpg.
Decrypt an Encrypted File
gpg <filename.gpg>
This will fail if you do not have the matching private key for the public key that was used to encrypt filename.gpg.
Setting Trust Level of Imported Public Key
You can set the trust level of an imported key using:
$ gpg --edit-key me@somewhere.com gpg> trust
This will present you with the trust level options:
1 = I don't know or won't say 2 = I do NOT trust 3 = I trust marginally 4 = I trust fully 5 = I trust ultimately m = back to the main menu
Remove or Add Private Key Password
$ gpg --edit-key me@somewhere.com gpg> passwd
Answer all the self-explanatory prompts, then:
gpg> quitStarting from Scratch
If, for whatever reason, you want to delete all your keys and start from scratch, you can simply delete your ~/.gnupg directory:
rm -rf ~/.gnupg
I have noticed on Ubuntu (and Ubuntu variants) that a required directory is not re-recreated when you do this and then try and generate your keys. If this happens, you’ll have to manually create the required directory and set the appropriate permissions:
$ mkdir -p ~/.gnupg/private-keys-v1.d $ chmod 700 ~/.gnupg/private-keys-v1.d $ gpg --gen-key
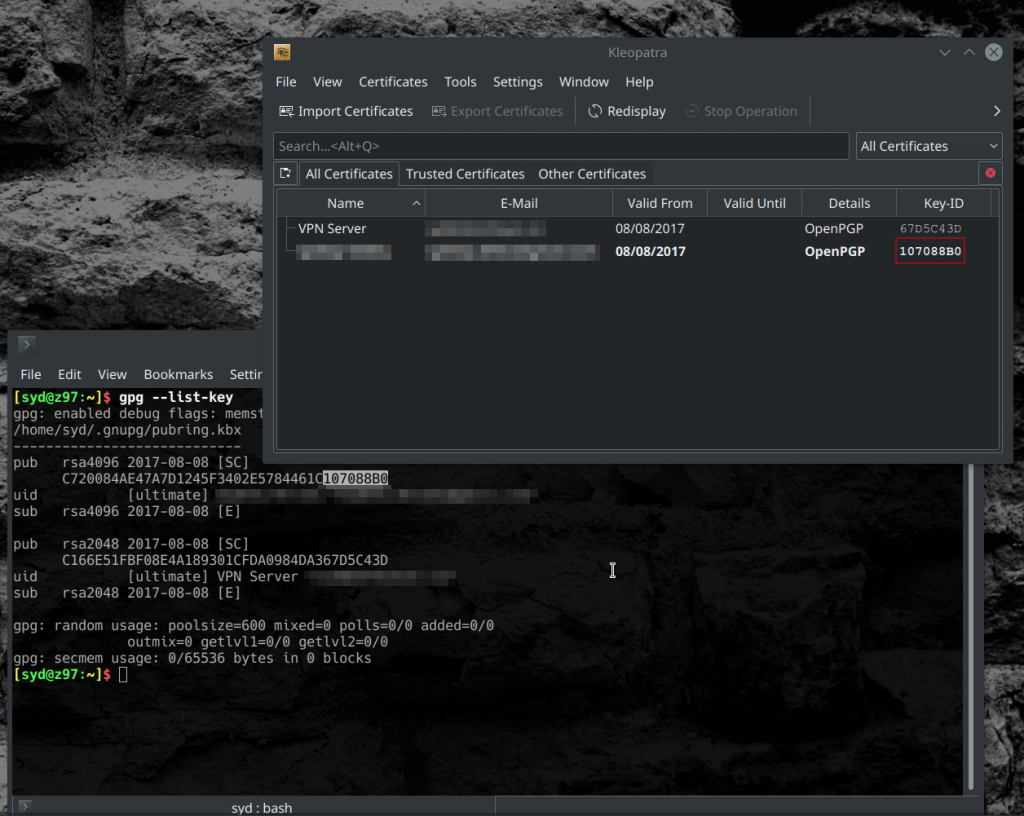
Using the Desktop GUI
In KDE Plasma 5, you can right-click on a file or folder to encrypt and sign it. This will only work if you have generated your keys and/or have imported the public keys of one or more recipients.
A program called Kleopatra provides a GUI front-end to OpenPGP and comes pre-installed on Kubuntu (and other KDE based distros). Just about any certificate operations you can perform from the terminal you can do using Kleopatra.
Other Thoughts
Encryption does not mean “secure forever” – it simply buys you time. Think about the computing power that will be available in 50 years time – in all likelihood, what we consider “strong” encryption today will probably take a few minutes to crack at some point in the future.
It should also be noted that in crypto schemes (like HTTPS, for example), asymmetrical cryptographic algorithms are only used to encrypt and share a key that is then used by a symmetrical algorithm. The main reason for this is speed – symmetrical crypto algorithms are orders of magnitude faster, and there are well known attacks against most asymmetrical crypto algorithms if there is a large amount of ciphertext available.
So stay away from ROT13, and ENCRYPT ALL THE THINGS!